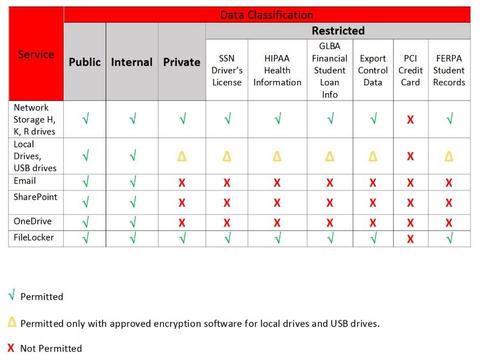
Quarterly Security Update: Storing Sensitive Data | CaTS | Information Technology | Wright State University
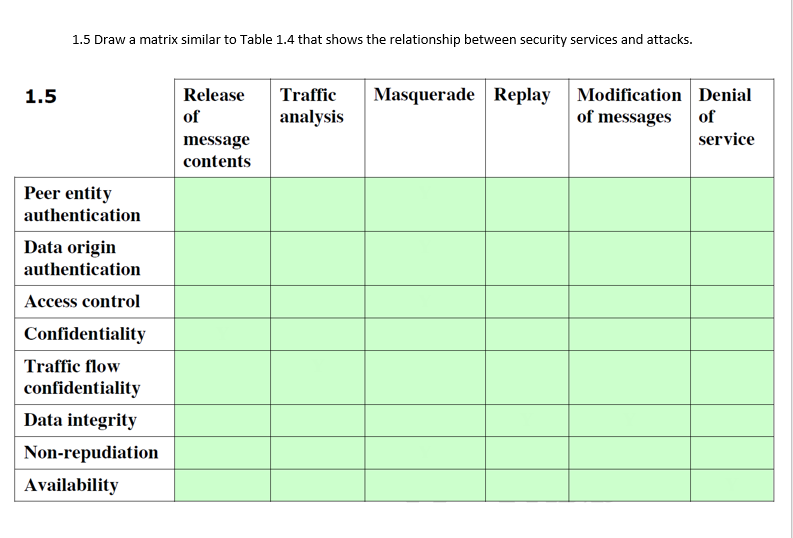
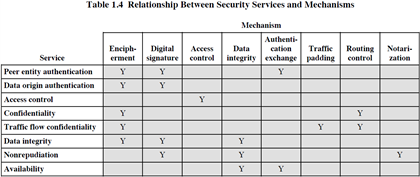
Considerations on Visible Light Communication security by applying the Risk Matrix methodology for risk assessment | PLOS ONE
Skill Matrix Table Identifying Technical Security And Transaction Processing | PowerPoint Slides Diagrams | Themes for PPT | Presentations Graphic Ideas

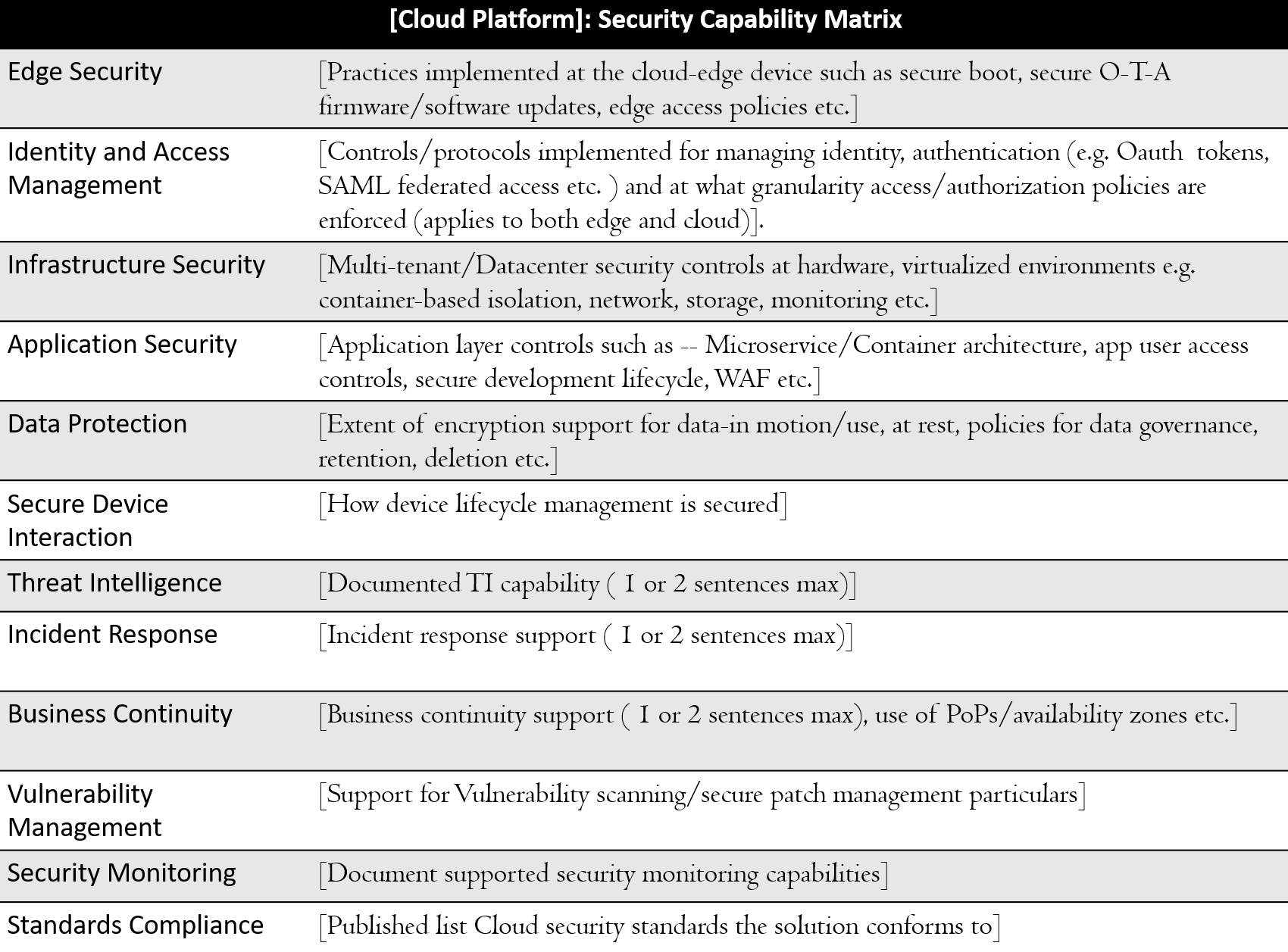
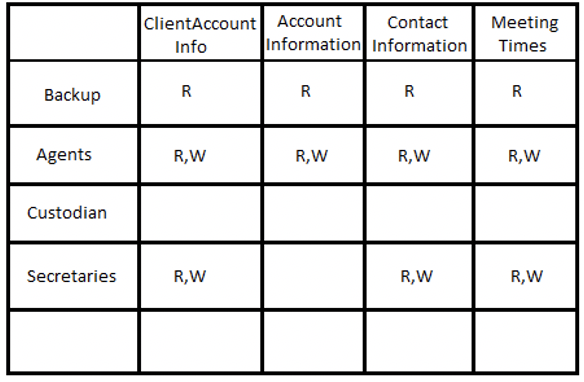
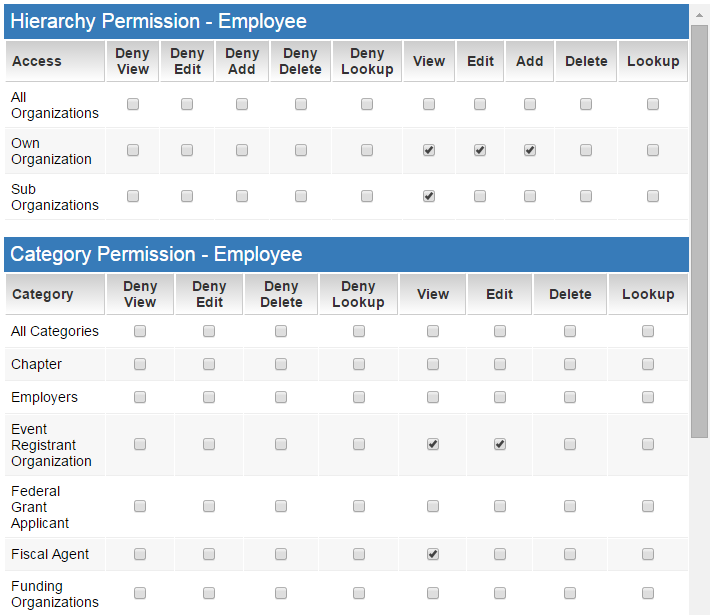
To improve the current security model and efficiency in cloud computing using access control matrix | Semantic Scholar

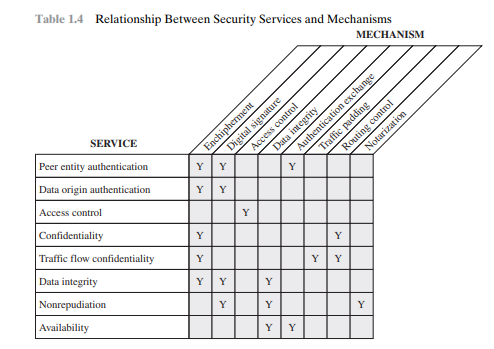
Matrix of the Internet Security Framework. The table shows security... | Download Scientific Diagram
Considerations on Visible Light Communication security by applying the Risk Matrix methodology for risk assessment | PLOS ONE

![Security+: risk management processes and concepts [updated 2021] | Infosec Resources Security+: risk management processes and concepts [updated 2021] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/Table3.png)