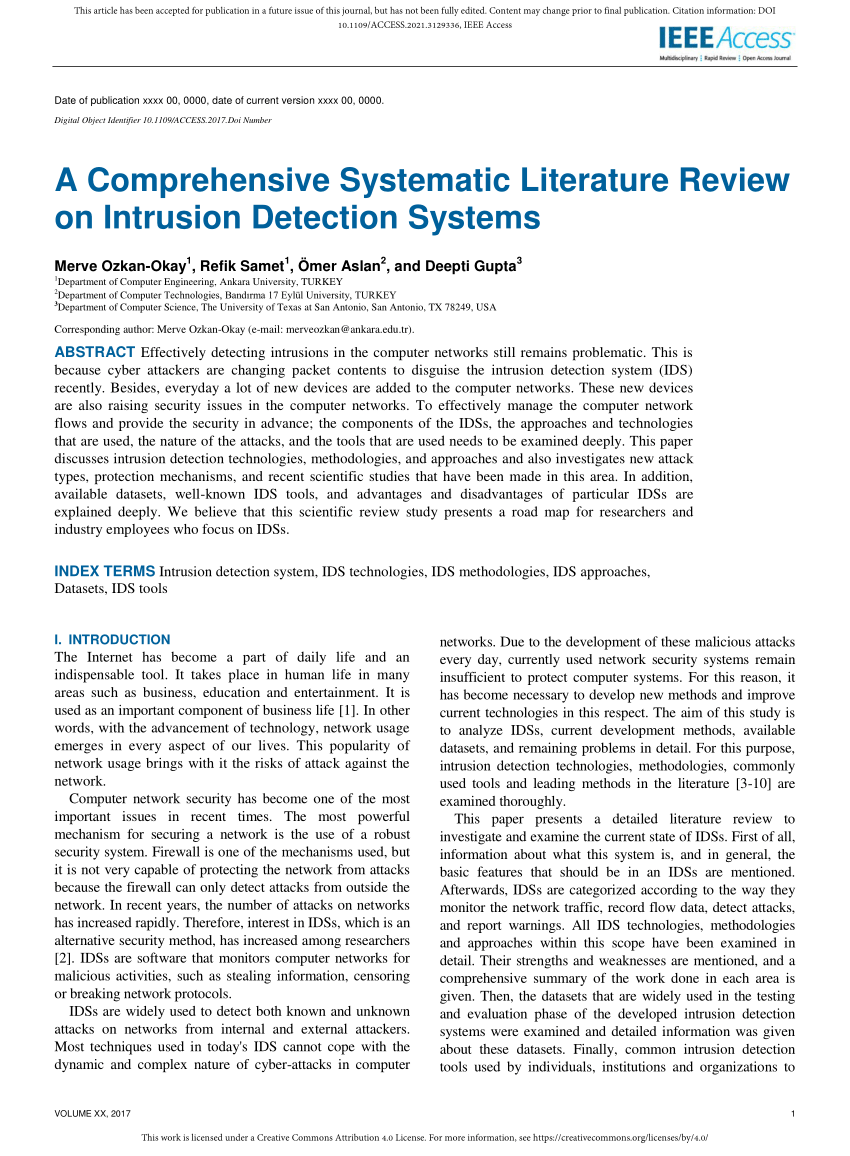
Anomaly network-based intrusion detection system using a reliable hybrid artificial bee colony and AdaBoost algorithms - ScienceDirect
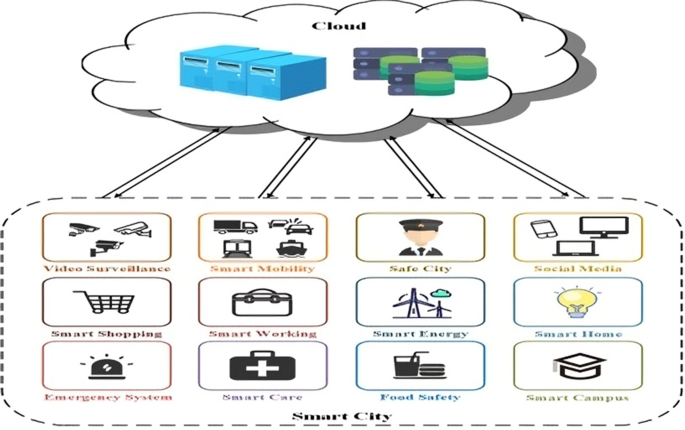
Design of Intrusion Detection System based on Cyborg intelligence for security of Cloud Network Traffic of Smart Cities | Journal of Cloud Computing | Full Text

PDF) Network intrusion detection system: A systematic study of machine learning and deep learning approaches

Anomaly‐based intrusion detection systems: The requirements, methods, measurements, and datasets - Hajj - 2021 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library

Anomaly‐based intrusion detection systems: The requirements, methods, measurements, and datasets - Hajj - 2021 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library

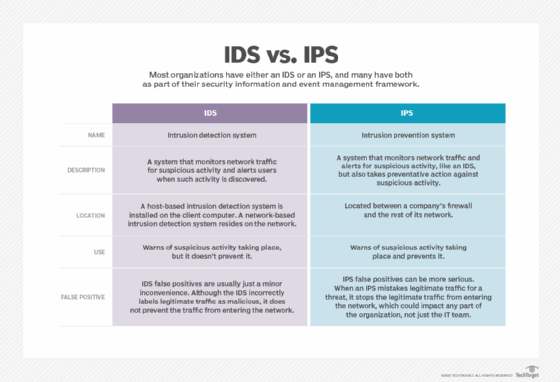
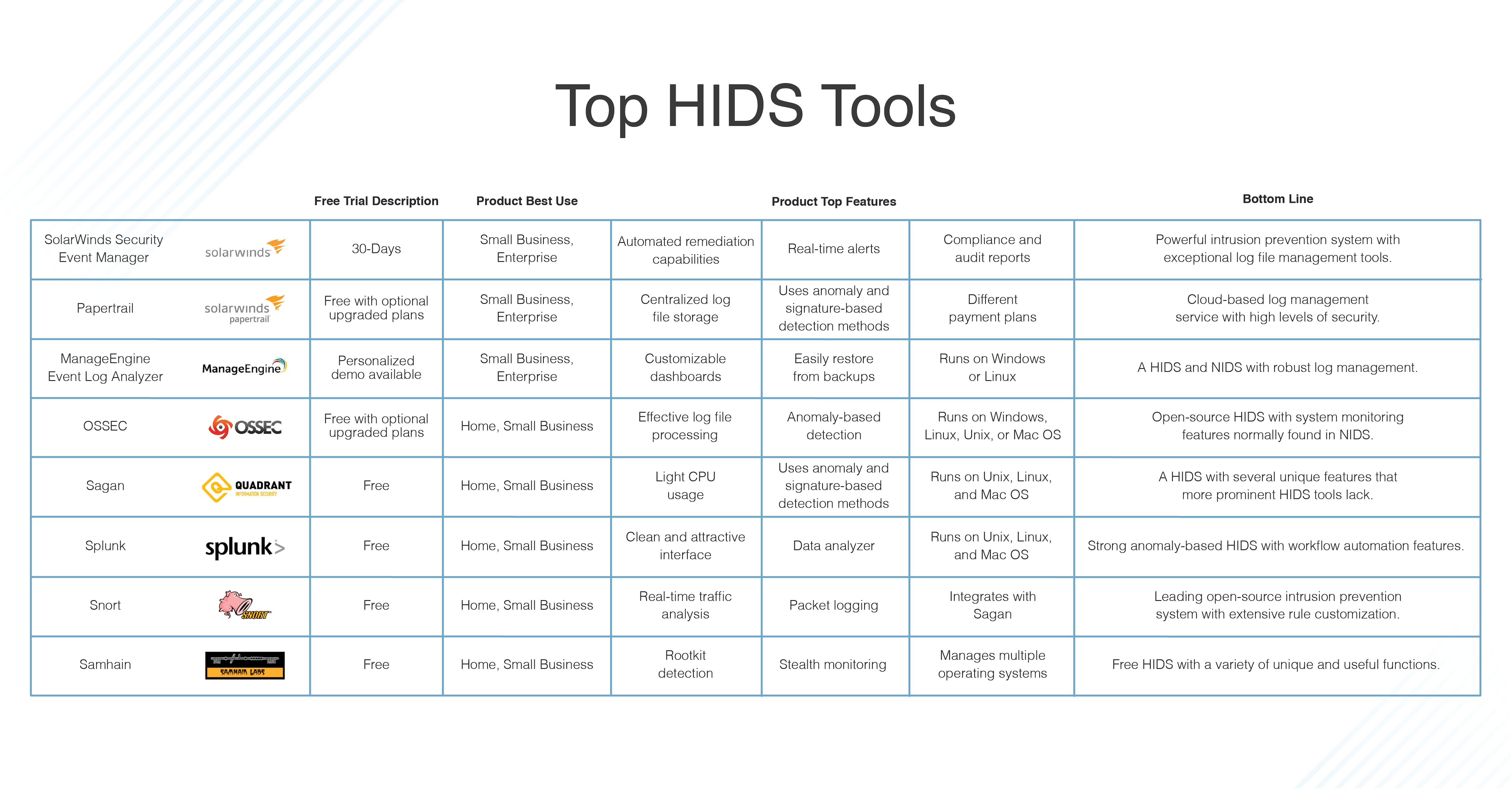
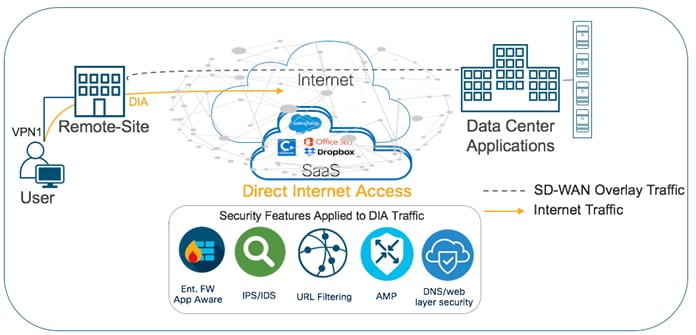
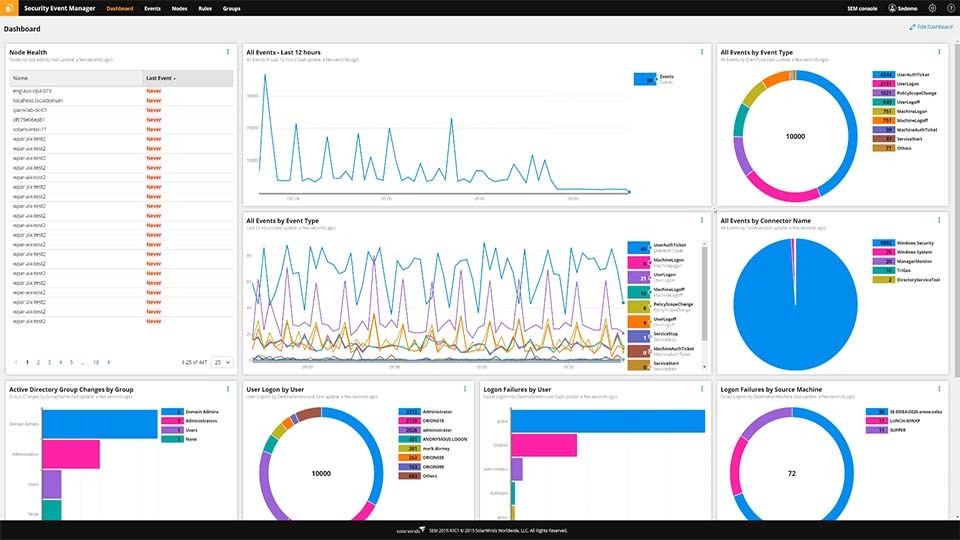
What Is Intrusion Detection and Prevention System? Definition, Examples, Techniques, and Best Practices | Spiceworks It Security

Anomaly‐based intrusion detection systems: The requirements, methods, measurements, and datasets - Hajj - 2021 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library